Akamai Bot Manager智能防护体系解析:边缘计算与AI驱动的反爬虫技术
深度剖析Akamai Bot Manager的边缘计算架构、机器学习检测引擎、实时威胁响应机制,为企业级反爬虫防护提供全面的技术洞察和实施策略。
{
“title”: “Akamai Bot Manager智能防护体系解析:边缘计算与AI驱动的反爬虫技术”,
“tags”: “Akamai,Bot Manager,边缘计算,反爬虫,CDN安全,机器学习,威胁检测,网络安全”,
“description”: “深度剖析Akamai Bot Manager的边缘计算架构、机器学习检测引擎、实时威胁响应机制,为企业级反爬虫防护提供全面的技术洞察和实施策略。”,
“author”: “技术专家”,
“date”: “2025-01-11”,
“category”: “网络安全”,
“keywords”: “Akamai,边缘计算,反爬虫,CDN,机器学习,威胁检测”,
“content”: "# Akamai Bot Manager智能防护体系解析:边缘计算与AI驱动的反爬虫技术
技术概述
Akamai Bot Manager作为全球领先的边缘安全解决方案,依托Akamai庞大的CDN网络,在全球130多个国家的4000+边缘服务器上提供实时威胁检测和防护服务。其独特的边缘计算架构使得安全检测能够在距离用户最近的节点执行,显著降低延迟的同时提供强大的防护能力。
核心技术优势
- 全球边缘部署:基于Akamai Intelligent Edge Platform的分布式防护
- 实时威胁情报:整合全球流量数据的机器学习威胁识别
- 零延迟检测:边缘节点本地化的安全决策机制
- 企业级防护:支持大规模高并发场景的商业化解决方案
边缘计算架构分析
1. 分布式安全决策引擎
Akamai Bot Manager在每个边缘节点部署独立的安全决策引擎,实现本地化威胁检测:
# Akamai边缘安全决策引擎模拟
import asyncio
import hashlib
from datetime import datetime
class EdgeSecurityEngine:
def __init__(self, node_id, geo_location):
self.node_id = node_id
self.geo_location = geo_location
self.threat_models = {}
self.local_cache = {}
self.global_reputation = {}
async def process_request(self, request):
"""边缘节点处理请求"""
# 快速本地检测
local_decision = await self.local_threat_detection(request)
if local_decision['action'] != 'ANALYZE':
return local_decision
# 深度分析
advanced_analysis = await self.advanced_threat_analysis(request)
# 全局威胁情报查询
reputation_check = await self.query_global_reputation(request)
# 综合决策
return self.make_final_decision([local_decision, advanced_analysis, reputation_check])
async def local_threat_detection(self, request):
"""本地威胁检测"""
risk_score = 0
# IP声誉检查
if request.client_ip in self.local_cache.get('blocked_ips', set()):
return {'action': 'BLOCK', 'reason': 'IP_REPUTATION', 'confidence': 0.95}
# 请求频率检查
request_rate = self.calculate_request_rate(request.client_ip)
if request_rate > 100: # 每秒超过100请求
risk_score += 0.6
# User-Agent异常检查
ua_anomaly = self.detect_ua_anomaly(request.user_agent)
risk_score += ua_anomaly * 0.3
# TLS指纹检查
tls_risk = self.analyze_tls_fingerprint(request.tls_fingerprint)
risk_score += tls_risk * 0.4
if risk_score > 0.8:
return {'action': 'BLOCK', 'reason': 'HIGH_RISK', 'confidence': risk_score}
elif risk_score > 0.5:
return {'action': 'CHALLENGE', 'reason': 'MEDIUM_RISK', 'confidence': risk_score}
else:
return {'action': 'ANALYZE', 'reason': 'DEEP_CHECK', 'confidence': risk_score}
2. 全球威胁情报网络
Akamai通过分析全球每日数万亿次请求,构建实时威胁情报数据库:
# 全球威胁情报系统
import redis
import json
from collections import defaultdict
class GlobalThreatIntelligence:
def __init__(self):
self.redis_client = redis.Redis(host='threat-intel.akamai.com', port=6379)
self.threat_categories = {
'credential_stuffing': 0.9,
'web_scraping': 0.7,
'ddos_amplification': 0.95,
'api_abuse': 0.6,
'account_takeover': 0.85
}
async def update_threat_intelligence(self, global_data):
"""更新全球威胁情报"""
threat_stats = defaultdict(int)
for edge_node in global_data:
for threat_type, count in edge_node['detected_threats'].items():
threat_stats[threat_type] += count
# 更新威胁趋势
await self.update_threat_trends(threat_stats)
# 同步到所有边缘节点
await self.sync_to_edge_nodes(threat_stats)
async def query_ip_reputation(self, ip_address):
"""查询IP声誉"""
cache_key = f"ip_reputation:{ip_address}"
cached_result = self.redis_client.get(cache_key)
if cached_result:
return json.loads(cached_result)
# 实时分析IP行为
reputation_data = await self.analyze_ip_behavior(ip_address)
# 缓存结果
self.redis_client.setex(cache_key, 300, json.dumps(reputation_data))
return reputation_data
async def analyze_ip_behavior(self, ip_address):
"""分析IP行为模式"""
behavior_metrics = {
'request_frequency': await self.get_request_frequency(ip_address),
'geographic_dispersion': await self.analyze_geo_dispersion(ip_address),
'protocol_compliance': await self.check_protocol_compliance(ip_address),
'session_behavior': await self.analyze_session_patterns(ip_address)
}
# 计算综合威胁分数
threat_score = sum(behavior_metrics.values()) / len(behavior_metrics)
return {
'ip_address': ip_address,
'threat_score': threat_score,
'risk_category': self.classify_risk(threat_score),
'behavior_metrics': behavior_metrics,
'last_updated': datetime.now().isoformat()
}
多层检测机制
1. JavaScript挑战验证
Akamai Bot Manager使用动态JavaScript挑战来区分真实浏览器和自动化工具:
// Akamai JavaScript挑战生成
class AkamaiJSChallenge {
constructor() {
this.challengeId = this.generateChallengeId();
this.startTime = Date.now();
}
generateChallengeId() {
const timestamp = Date.now();
const randomBytes = new Uint8Array(16);
crypto.getRandomValues(randomBytes);
return btoa(timestamp + Array.from(randomBytes).join(''));
}
createDynamicChallenge() {
const challenges = [
this.domManipulationChallenge(),
this.webglContextChallenge(),
this.canvasRenderingChallenge(),
this.mousemovementChallenge()
];
return {
challengeId: this.challengeId,
challenges: challenges,
timeout: 30000
};
}
domManipulationChallenge() {
return {
type: 'dom_manipulation',
task: () => {
// 创建隐藏元素并获取计算样式
const testElement = document.createElement('div');
testElement.style.cssText = 'opacity:0;position:absolute;top:-9999px;';
testElement.innerHTML = '测试内容';
document.body.appendChild(testElement);
const computedStyle = window.getComputedStyle(testElement);
const result = computedStyle.opacity + computedStyle.position;
document.body.removeChild(testElement);
return btoa(result);
}
};
}
webglContextChallenge() {
return {
type: 'webgl_context',
task: () => {
const canvas = document.createElement('canvas');
const gl = canvas.getContext('webgl') || canvas.getContext('experimental-webgl');
if (!gl) return 'NO_WEBGL';
const renderer = gl.getParameter(gl.RENDERER);
const vendor = gl.getParameter(gl.VENDOR);
return btoa(renderer + vendor);
}
};
}
async executeChallenges() {
const results = [];
const challenges = this.createDynamicChallenge();
for (const challenge of challenges.challenges) {
try {
const result = await challenge.task();
results.push({
type: challenge.type,
result: result,
timestamp: Date.now()
});
} catch (error) {
results.push({
type: challenge.type,
error: error.message,
timestamp: Date.now()
});
}
}
return this.submitChallengeResults(results);
}
}
2. 行为生物识别技术
Akamai采用先进的行为生物识别技术,分析用户的鼠标移动、键盘输入、触摸模式等行为特征:
# 行为生物识别分析
import numpy as np
from scipy import signal
from sklearn.cluster import DBSCAN
class BehaviorBiometricsAnalyzer:
def __init__(self):
self.mouse_patterns = []
self.keyboard_patterns = []
self.touch_patterns = []
def analyze_mouse_dynamics(self, mouse_events):
"""分析鼠标动力学特征"""
if len(mouse_events) < 10:
return {'confidence': 0, 'is_human': False}
# 提取运动特征
velocities = self.calculate_velocities(mouse_events)
accelerations = self.calculate_accelerations(velocities)
# 分析移动轨迹的复杂性
trajectory_complexity = self.analyze_trajectory_complexity(mouse_events)
# 检测人类特有的微颤动
tremor_analysis = self.analyze_tremor_patterns(mouse_events)
# 计算人类行为可能性
human_likelihood = self.calculate_human_likelihood({
'velocity_variance': np.var(velocities),
'acceleration_distribution': self.analyze_distribution(accelerations),
'trajectory_complexity': trajectory_complexity,
'tremor_score': tremor_analysis
})
return {
'confidence': human_likelihood,
'is_human': human_likelihood > 0.7,
'features': {
'velocity_stats': np.mean(velocities),
'trajectory_entropy': trajectory_complexity,
'tremor_presence': tremor_analysis > 0.3
}
}
def calculate_velocities(self, mouse_events):
"""计算鼠标移动速度"""
velocities = []
for i in range(1, len(mouse_events)):
dx = mouse_events[i]['x'] - mouse_events[i-1]['x']
dy = mouse_events[i]['y'] - mouse_events[i-1]['y']
dt = mouse_events[i]['timestamp'] - mouse_events[i-1]['timestamp']
if dt > 0:
velocity = np.sqrt(dx**2 + dy**2) / dt
velocities.append(velocity)
return np.array(velocities)
def analyze_keyboard_dynamics(self, keyboard_events):
"""分析键盘输入动力学"""
if len(keyboard_events) < 5:
return {'confidence': 0, 'is_human': False}
# 计算按键间隔时间
inter_key_intervals = []
dwell_times = []
for i in range(1, len(keyboard_events)):
if keyboard_events[i]['type'] == 'keydown':
interval = keyboard_events[i]['timestamp'] - keyboard_events[i-1]['timestamp']
inter_key_intervals.append(interval)
if (keyboard_events[i]['type'] == 'keyup' and
keyboard_events[i-1]['type'] == 'keydown' and
keyboard_events[i]['key'] == keyboard_events[i-1]['key']):
dwell_time = keyboard_events[i]['timestamp'] - keyboard_events[i-1]['timestamp']
dwell_times.append(dwell_time)
# 分析打字节奏模式
rhythm_analysis = self.analyze_typing_rhythm(inter_key_intervals)
# 检测人类打字特征
human_score = self.calculate_typing_human_score({
'interval_variance': np.var(inter_key_intervals),
'dwell_consistency': np.std(dwell_times),
'rhythm_pattern': rhythm_analysis
})
return {
'confidence': human_score,
'is_human': human_score > 0.65,
'typing_speed': len(keyboard_events) / (keyboard_events[-1]['timestamp'] - keyboard_events[0]['timestamp']) * 1000
}
机器学习威胁识别
1. 实时异常检测引擎
Akamai使用先进的机器学习算法进行实时威胁检测:
# 实时异常检测系统
from tensorflow import keras
import pandas as pd
from sklearn.preprocessing import StandardScaler
class RealTimeAnomalyDetector:
def __init__(self):
self.autoencoder = self.build_autoencoder()
self.scaler = StandardScaler()
self.threshold = 0.02
def build_autoencoder(self):
"""构建自编码器异常检测模型"""
input_dim = 50 # 特征维度
input_layer = keras.layers.Input(shape=(input_dim,))
encoded = keras.layers.Dense(32, activation='relu')(input_layer)
encoded = keras.layers.Dense(16, activation='relu')(encoded)
encoded = keras.layers.Dense(8, activation='relu')(encoded)
decoded = keras.layers.Dense(16, activation='relu')(encoded)
decoded = keras.layers.Dense(32, activation='relu')(decoded)
output_layer = keras.layers.Dense(input_dim, activation='sigmoid')(decoded)
autoencoder = keras.Model(input_layer, output_layer)
autoencoder.compile(optimizer='adam', loss='mse')
return autoencoder
def extract_request_features(self, request):
"""提取请求特征向量"""
features = []
# 基础请求特征
features.extend([
len(request.get('user_agent', '')),
len(request.get('referer', '')),
request.get('content_length', 0),
len(request.get('headers', {}))
])
# 行为特征
behavior_data = request.get('behavior', {})
features.extend([
behavior_data.get('mouse_movements', 0),
behavior_data.get('keyboard_events', 0),
behavior_data.get('scroll_events', 0),
behavior_data.get('click_events', 0)
])
# 时间特征
features.extend([
request.get('session_duration', 0),
request.get('page_load_time', 0),
request.get('request_interval', 0)
])
# TLS特征
tls_features = request.get('tls', {})
features.extend([
len(tls_features.get('cipher_suites', [])),
len(tls_features.get('extensions', [])),
tls_features.get('version', 0)
])
# 补充特征到50维
while len(features) < 50:
features.append(0)
return np.array(features[:50])
def detect_anomaly(self, request):
"""检测请求异常"""
features = self.extract_request_features(request)
features_scaled = self.scaler.transform([features])
# 通过自编码器重构
reconstructed = self.autoencoder.predict(features_scaled)
# 计算重构误差
mse = np.mean(np.power(features_scaled - reconstructed, 2))
is_anomaly = mse > self.threshold
confidence = min(1.0, mse / self.threshold)
return {
'is_anomaly': is_anomaly,
'anomaly_score': mse,
'confidence': confidence,
'features_analyzed': len(features)
}
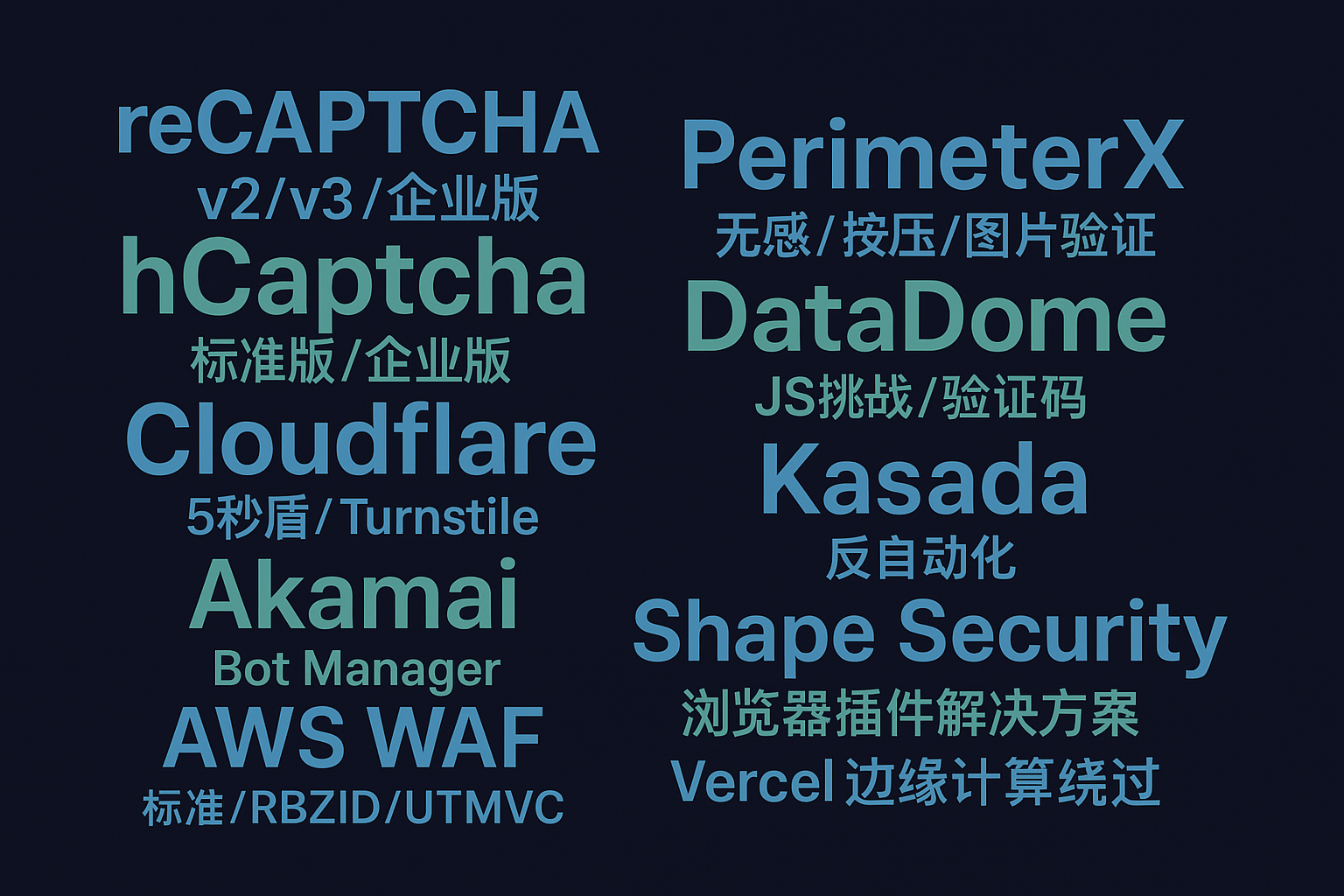
专业的WAF防护绕过需要深入理解各种防护机制的技术原理。Cloudflare 5秒盾专业绕过 - WAF防护一站式解决方案提供了针对多种WAF系统的专业绕过服务,通过智能分析和自动化技术,能够有效应对Akamai等高级防护系统。
实时响应与缓解策略
1. 动态限流算法
# 动态限流系统
import time
from collections import defaultdict
class DynamicRateLimiting:
def __init__(self):
self.client_buckets = defaultdict(lambda: {'tokens': 100, 'last_refill': time.time()})
self.global_buckets = defaultdict(lambda: {'tokens': 10000, 'last_refill': time.time()})
self.adaptive_limits = {}
def check_rate_limit(self, client_id, endpoint, risk_score=0.0):
"""检查速率限制"""
current_time = time.time()
# 获取客户端令牌桶
client_bucket = self.client_buckets[client_id]
# 基于风险分数调整限制
base_limit = 100
adjusted_limit = max(10, base_limit * (1 - risk_score))
# 令牌桶填充
time_passed = current_time - client_bucket['last_refill']
tokens_to_add = int(time_passed * (adjusted_limit / 60)) # 每分钟填充
client_bucket['tokens'] = min(adjusted_limit, client_bucket['tokens'] + tokens_to_add)
client_bucket['last_refill'] = current_time
# 检查是否有可用令牌
if client_bucket['tokens'] > 0:
client_bucket['tokens'] -= 1
return {
'allowed': True,
'remaining_tokens': client_bucket['tokens'],
'reset_time': current_time + 60
}
else:
return {
'allowed': False,
'retry_after': 60,
'reason': 'RATE_LIMITED'
}
def adaptive_limit_adjustment(self, global_traffic_stats):
"""自适应限制调整"""
for endpoint, stats in global_traffic_stats.items():
current_rps = stats.get('requests_per_second', 0)
error_rate = stats.get('error_rate', 0)
# 根据错误率调整限制
if error_rate > 0.1: # 错误率超过10%
self.adaptive_limits[endpoint] = 0.5 # 降低50%限制
elif error_rate < 0.01: # 错误率低于1%
self.adaptive_limits[endpoint] = min(2.0, self.adaptive_limits.get(endpoint, 1.0) * 1.1)
2. 智能缓存策略
# 智能缓存防护
class IntelligentCacheProtection:
def __init__(self):
self.cache_rules = {}
self.threat_cache = {}
self.legitimate_cache = {}
def determine_cache_strategy(self, request, threat_analysis):
"""确定缓存策略"""
if threat_analysis['risk_score'] > 0.8:
# 高风险请求,缓存阻断响应
return {
'cache_type': 'threat_response',
'ttl': 3600, # 1小时
'response': self.generate_block_response()
}
elif threat_analysis['risk_score'] < 0.2:
# 低风险请求,正常缓存
return {
'cache_type': 'normal',
'ttl': 300, # 5分钟
'bypass_protection': True
}
else:
# 中等风险,不缓存,每次检测
return {
'cache_type': 'no_cache',
'force_validation': True
}
防护策略建议
1. 分层防护配置
# Akamai Bot Manager配置示例
bot_manager_config:
detection_modes:
- javascript_challenge
- behavior_analysis
- reputation_check
- ml_anomaly_detection
response_actions:
block:
threshold: 0.9
duration: 3600
challenge:
threshold: 0.6
type: javascript
timeout: 30
monitor:
threshold: 0.3
log_level: INFO
custom_rules:
- name: "API_Protection"
path: "/api/*"
rate_limit: 100/minute
require_authentication: true
- name: "Login_Protection"
path: "/login"
enhanced_detection: true
challenge_always: true
2. 监控与告警
# 威胁监控系统
class ThreatMonitoring:
def __init__(self, alert_webhook):
self.alert_webhook = alert_webhook
self.threat_thresholds = {
'requests_per_second': 1000,
'blocked_percentage': 0.1,
'new_attack_patterns': 5
}
async def monitor_threats(self, time_window=60):
"""监控威胁趋势"""
current_metrics = await self.collect_metrics(time_window)
alerts = []
for metric, threshold in self.threat_thresholds.items():
if current_metrics.get(metric, 0) > threshold:
alerts.append({
'type': 'THRESHOLD_EXCEEDED',
'metric': metric,
'current_value': current_metrics[metric],
'threshold': threshold,
'timestamp': datetime.now().isoformat()
})
if alerts:
await self.send_alerts(alerts)
return current_metrics
技术发展趋势
Akamai Bot Manager正在向更加智能化和自动化的方向发展:
1. 零信任安全模型
未来将采用零信任架构,对每个请求都进行全面的安全评估,不再基于传统的网络边界概念。
2. 量子安全加密
随着量子计算技术的发展,Akamai正在研发抗量子攻击的加密算法,确保长期安全性。
3. 边缘AI计算
在边缘节点部署更强大的AI模型,实现毫秒级的威胁检测和响应。
边缘计算驱动的智能安全防护 - 为全球企业提供可靠保障
结语
Akamai Bot Manager通过其独特的边缘计算架构和AI驱动的威胁检测技术,为企业提供了强大的反爬虫和安全防护能力。其全球分布式的部署模式不仅保证了高性能,更实现了近乎实时的威胁响应。对于企业级应用而言,理解和正确配置这些高级安全功能,是构建现代化安全防护体系的关键。随着威胁环境的不断演变,Akamai也在持续创新,为网络安全领域带来更多突破性的技术解决方案。
关键词标签: Akamai Bot Manager, 边缘计算, CDN安全, 反爬虫, 机器学习, 威胁检测, 行为分析, 实时防护, 企业安全, 智能缓存",
更多推荐
 已为社区贡献25条内容
已为社区贡献25条内容






所有评论(0)